Impersonation Attack
Learn what impersonation attacks are, how scammers exploit trust, and how to verify identities in Web3.

What Is an Impersonation Attack?
An impersonation or pretext attack is a social engineering scam where criminals pretend to be someone you trust, like customer support, a company executive, or a well-known crypto personality, to trick you into taking harmful actions. These attacks exploit trust rather than technical vulnerabilities, making them especially dangerous.
How It Works

Scammers craft believable scenarios designed to create urgency and bypass your skepticism. Common tactics include fake security alerts (“Your wallet has been compromised, click here immediately!”), phony support messages on Discord or Telegram, or impersonating executives on video calls.
They’ll even create lookalike social media accounts, spoof email addresses, or use AI to clone voices and faces.
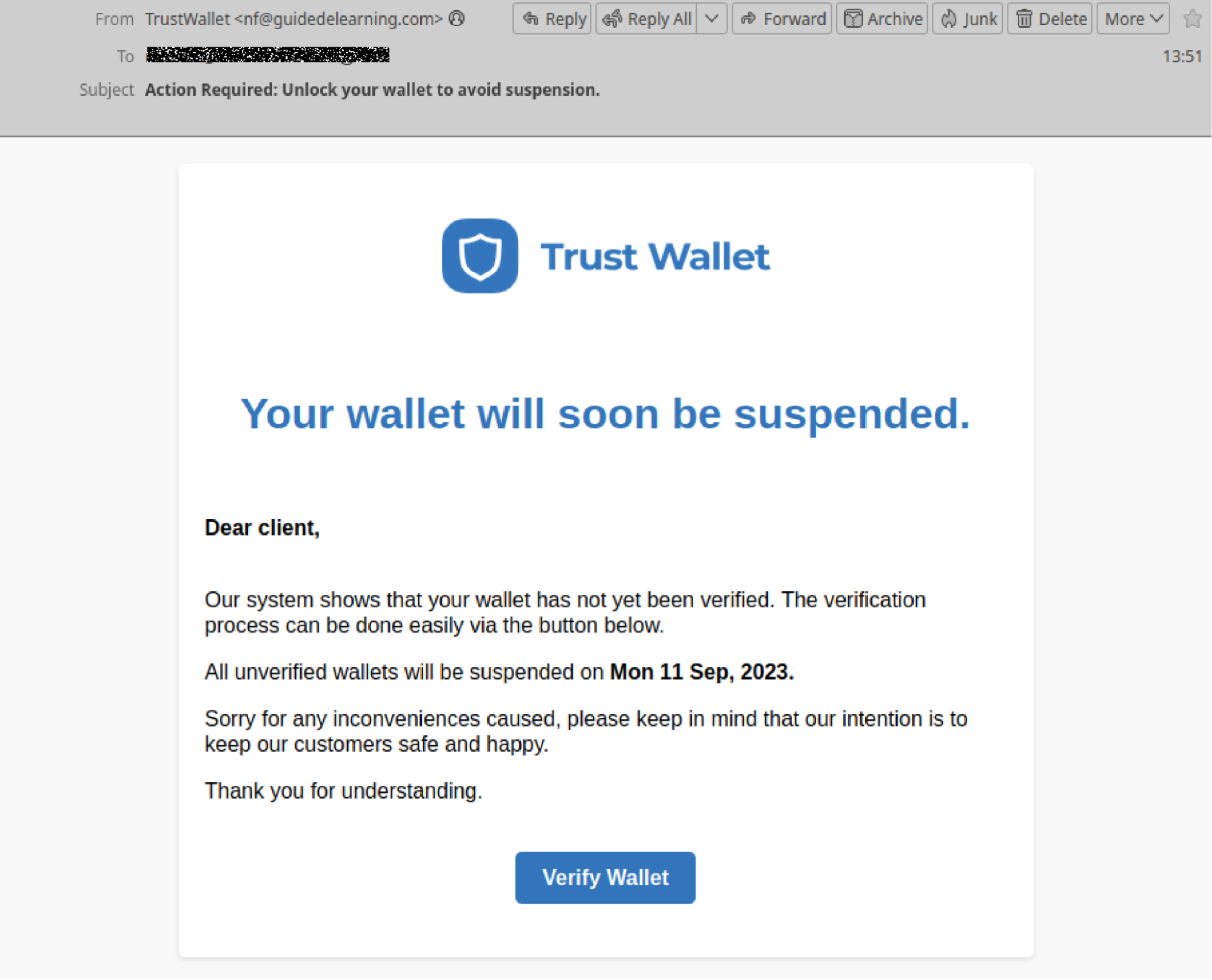
Source: Mailguard
One specific ploy that I experienced personally was a request form a popular X account to be featured in a Coindesk podcast last year. The conversation was soon moved to a Telegram chat with other attendees, who were all impersonators. Their goal was to get me to install “video conferencing” malware which would allow them to access my computer and steal my funds without any detection.
The goal is always the same: get you to reveal sensitive information, approve malicious wallet transactions, or visit fake websites that drain your funds.
These scams frequently funnel victims toward crypto wallet drainer sites that empty accounts in seconds once you approve a transaction.
Why It Matters
Impersonation attacks scale trust exploitation to industrial levels. In 2024 and 2025, AI-enhanced campaigns using deepfake voices and cloned social media profiles targeted crypto founders, exchange customers, and DeFi users, resulting in millions in losses.
One sophisticated attack involved scammers impersonating a project’s entire support team, complete with matching profile pictures and conversation histories, to steal user funds over several weeks.
The attacks are becoming harder to detect as AI tools make fake identities more convincing. Even experienced crypto users have fallen victim to well-executed impersonation scams.
How to Protect Yourself
-
Always verify identities through official channels, if someone claims to be support, contact the company directly using verified contact information, not links they provide
-
Remember that legitimate companies never ask for seed phrases or private keys
-
Be suspicious of urgent requests, especially those pressuring immediate action
-
Understanding Web3 social engineering and phishing patterns is your first line of defense against these trust-based attacks
-
Use Web3 security tools like Kerberus and Pocket Universe to get real-time protection and warnings when interacting with Web3 platforms
-
Check Kerberus Learn academy for top crypto safety information
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Terms
See more glossary termsInstall once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.




